Zero TrustPlatforms
We leverage leading Zero Trust platforms to enforce identity-based access and continuous verification across your environment integrated into your architecture and operated as part of your overall security strategy.
These platforms eliminate implicit trust by validating every user, device, and session before granting access to applications and data.
Capabilities enabled:
- Identity-based access control and least-privilege enforcement
- Continuous verification based on user, device, and context
- Device posture and compliance checks
- Micro-segmentation to prevent lateral movement
- Secure access to private applications without VPNs
How IPS uses these platforms
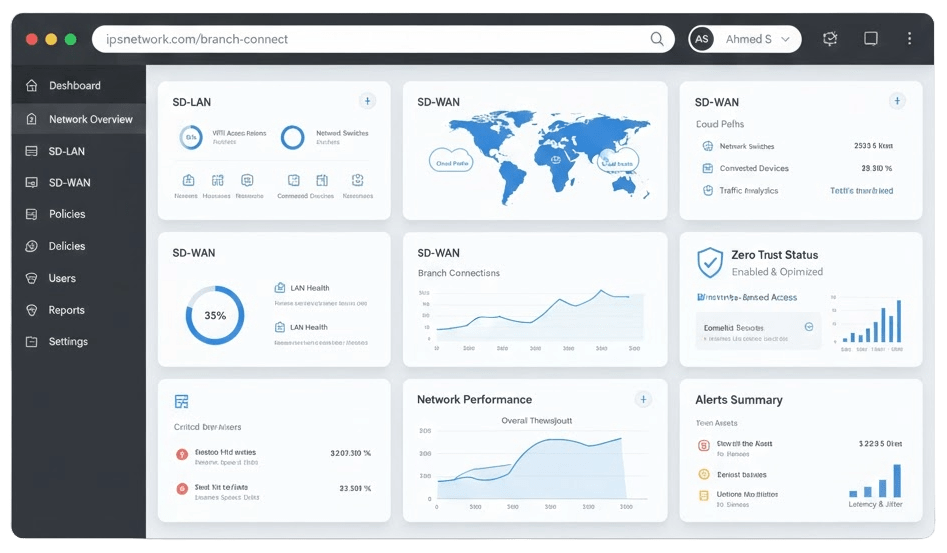
We design, deploy, and manage Zero Trust architectures aligned to your business—integrating identity providers, endpoints, and applications while continuously refining policies to strengthen security and user experience.
Technology partners
- Palo Alto Networks
- Cisco
- Fortinet

